Structured Cabling
 A structured cabling system is a complete system of cabling and associated hardware, which provides a comprehensive telecommunications infrastructure. This infrastructure serves a wide range of uses, such as to provide telephone service or transmit data through a computer network. It should not be device dependent.
A structured cabling system is a complete system of cabling and associated hardware, which provides a comprehensive telecommunications infrastructure. This infrastructure serves a wide range of uses, such as to provide telephone service or transmit data through a computer network. It should not be device dependent.
Your business networks and communications depend on the quality of your cabling and wiring. Red I.T. Solutions provides professional cabling and wiring services and systems that will give you exceptional performance, manageability, reliability, and scalability.
Our professional Wiring technicians can tackle any small or large project:
- Network cabling – we can design a new office layout or document an existing topology of your infrastructure
- Cable and wiring repair – diagnosis and repair of problems at your patch panel or desk location
- Move adds or changes – for any incremental changes to your system
- Core infrastructure cabling – for building or office backbone connections
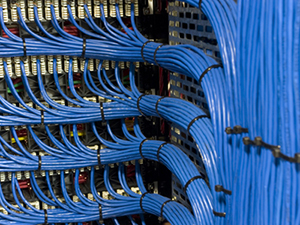
- Server rack cabling – organized, labeled, and professionally organized
- Rack installs - for new rack installations include power and UPS systems
Physical Security
 Access control systems provide authorized individuals safe and secure access in and out of various parts of your business while keeping unauthorized people out. They can range from electronic keypads that secure a single door to large networked systems for multiple buildings. Access Systems also greatly simplify management of your facility: no need to replace lost keys, hunt down old keys from terminated employees, or wonder who has access to which areas.
Access control systems provide authorized individuals safe and secure access in and out of various parts of your business while keeping unauthorized people out. They can range from electronic keypads that secure a single door to large networked systems for multiple buildings. Access Systems also greatly simplify management of your facility: no need to replace lost keys, hunt down old keys from terminated employees, or wonder who has access to which areas.
The most basic role of an access control system is to keep out anyone who is not supposed to enter an area. This can be the front door, a parking garage, a server room, a personnel records room, or any other sensitive area. Items to considered:
- You may also want to use an access control system to track when employees come and go.
- How secure do you need the system to be? A basic system usually features a keypad or swipe card. Higher security applications may require multiple means of authentication (a card and thumbprint, for example) and include more redundancy.
- Finally, consider what other systems need to connect to your access control system. Monitored alarm systems and CCTV systems are two good examples.
We can install most Manufacturer and Vendor solutions of IP Cameras and Door Access Control Systems.